Security
Article originally written by ATI partner AT&T BusinessIs your organization prepared? Is your security maturity advancing? Are you concerned with meeting compliance privacy regulations? At AT&T, we help organizations minimize risks, manage security operations effectively and work toward meeting compliance requirements.
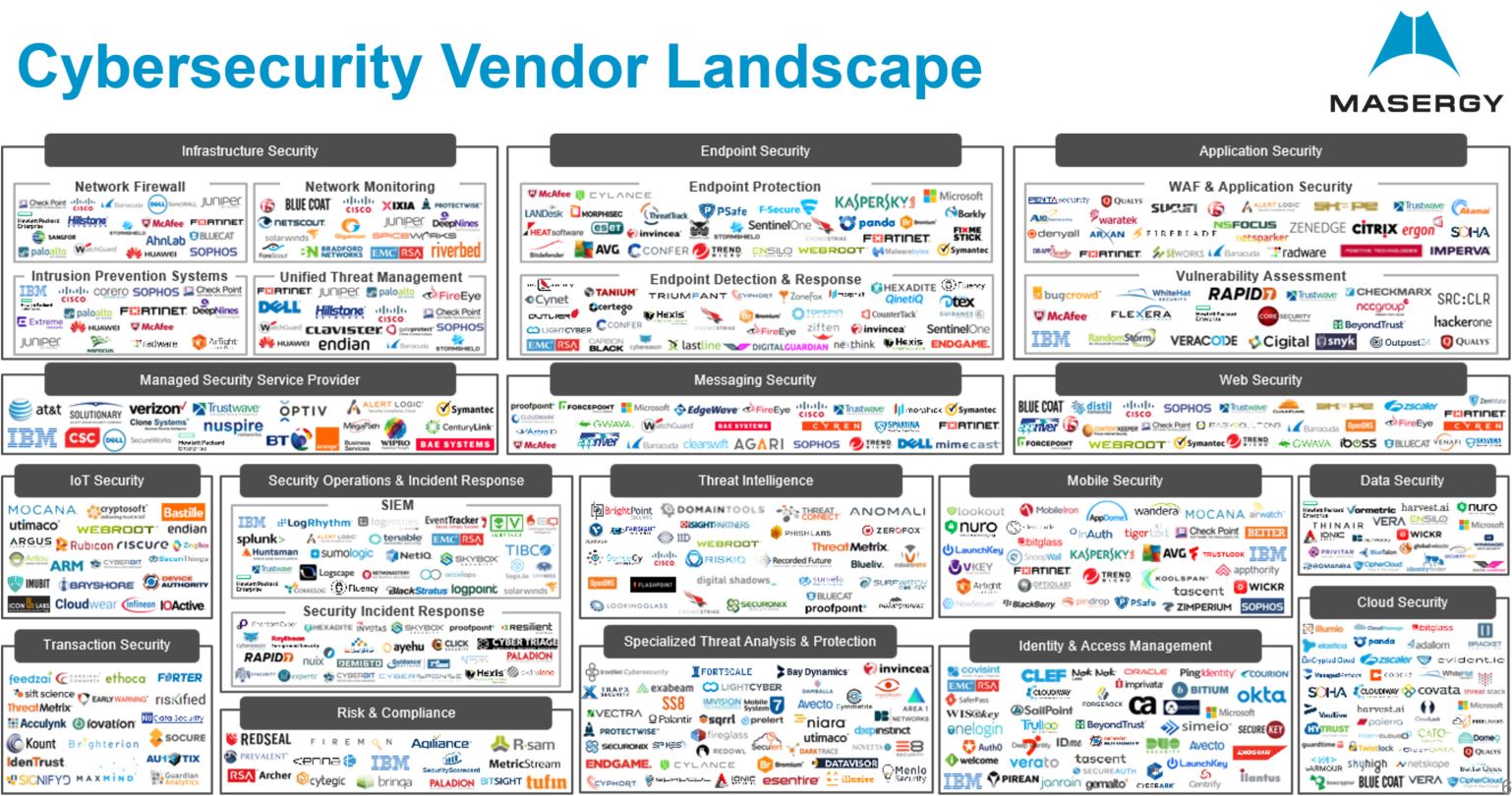
Organizations often struggle to get the visibility they need to truly understand their cyber risks and to address regulatory compliance requirements. What’s more, organizations struggle to maintain this visibility as their environments and risks change with new digital business transformation and cloud computing initiatives. This is especially true for organizations with limited IT resources. IT-constrained organizations often juggle multiple security products and vendors to address cyber risks and compliance, while also managing internal security policies and working to stay on top of changes in the regulatory landscape. And, they’re managing this amid their own, continuous network changes and a shifting threat landscape.
With unrivaled visibility across data, network and devices, leading insights from AT&T Alien Labs and our open source threat exchange, we can anticipate and act on threats to protect your business. We’re delivering a new era of transparency, giving you confidence in your decisions, your data, and your partnerships.
Every organization’s security program is unique in its maturity, architecture, resources, and risk tolerance. All too often, products and services for cyber risk and compliance management are packaged and priced exclusively for large enterprises. They are often rigid and do not easily adapt to your existing program or business objectives. AT&T Cybersecurity offers flexible solutions and services that align to the goals and budgets of your organization, while making it simple and fast to purchase, deploy, and get started. Select any product or combination of products to meet your needs and budget, and choose a deployment model that best suits your IT resourcing, either self-managed or as a co- or fully managed security service.